Minor Quantum Safe Cryptography
Starts in September
Sign up via Progress- 30 ECTS
- 20 weeks
- Fontys Applied Mathematics
About this minor
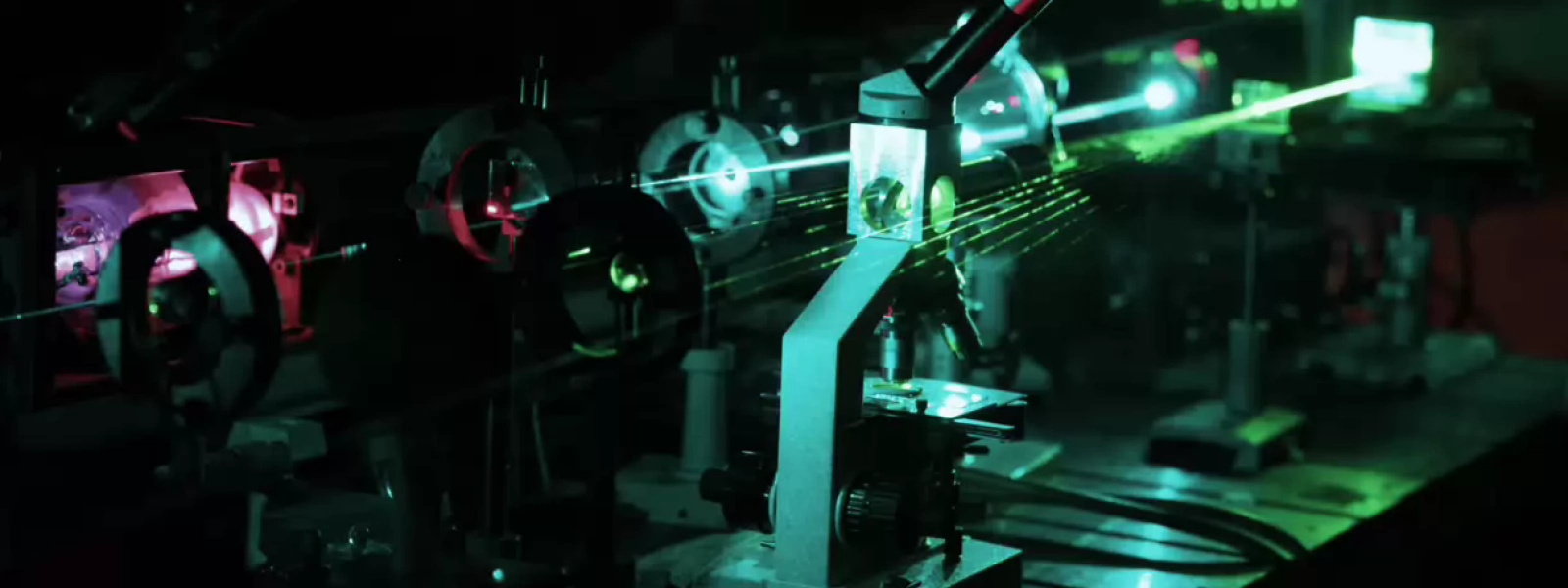
The Minor Quantum Safe Cryptography dives into one of the most urgent challenges in cybersecurity: preparing digital systems for the age of quantum computing. You explore both sides of the problem, software and hardware, and develop skills in high demand worldwide. On the software side, you study classical cryptography and post-quantum algorithms. On the hardware side, you work hands-on with a real Quantum Key Distribution setup, a rare opportunity within a university of applied sciences.
Why choose the minor Quantum Safe Cryptography?
- You work with real quantum hardware
- You contribute to research into tomorrow's security infrastructure
- Strongly multidisciplinary: software, hardware and mathematics combined
- Direct connection to Fontys research and applied industry challenges
More about the minor
Quantum computers are developing faster than most organisations realise. Once sufficiently powerful machines exist, today's encryption standards — RSA, ECC, AES — will no longer hold. The EU and major governments are already standardising post-quantum cryptography. Organisations urgently need professionals who understand both the threat and the solutions. In this minor, you develop the expertise organisations urgently need: you leave with practical, portfolio-worthy skills in PQC implementation and quantum key distribution.
- Analysis and implementation of post-quantum cryptographic algorithms (e.g. lattice-based cryptography)
- Hands-on work with a Quantum Key Distribution (BB84 / E-91) hardware setup
- Security analysis of cryptographic applications and threat modelling
- Guest lectures by experts from the quantum and security industry
The future of data security
Become the expert on the next defining computing technology!Programme
Core knowledge
- How quantum computers work (conceptual level)
- Why current cryptography is becoming vulnerable
- Post-Quantum Cryptography — lattice-based and other schemes
- Quantum Key Distribution: BB84 and E-91 protocols
- Cryptographic standards and security evaluation
Skills you develop
- Analyse and implement PQC algorithms
- Assess security risks posed by quantum threats
- Technically evaluate cryptographic solutions
- Integrate hardware and software into a secure system
- Interpret scientific publications in the field
- Apply security-by-design principles in practice
- Individual programming assignments and portfolio (15 ECTS)
- Group hardware project — QKD implementation (15 ECTS)
- Technical report (IEEE-paper format) and academic poster
- Oral presentation or live demo
There is a strong emphasis on technical depth and substantiated reasoning throughout all assessments.
- 3–4 contact days per week on campus (Engineering environment)
- Combination of lectures, lab sessions and project work
- Fixed class days plus project days
- Peak periods: algorithm deadlines, hardware integration, final presentations
This minor is closely connected to applied research at Fontys Engineering. Research themes include quantum communication, random number generators, and post-quantum implementations. All of which directly feed into the minor's content.
You contribute to:
- Validation of cryptographic implementations
- Performance analysis of PQC algorithms
- Testing hardware RNG solutions
- Experiments with QKD setups
Pathway to further work
This minor is a direct springboard into internships in cybersecurity or quantum technology, graduation projects in cryptography or secure systems, and research projects within Fontys. It is both education and a first step into applied research.
Digital security underpins everything: healthcare data, financial systems, government communication, and critical infrastructure. The transition to quantum-safe cryptography is a national and European priority, and organisations across every sector are seeking professionals to lead it.
By completing this minor, you contribute to:
- Protection of digital infrastructure
- Secure communication in a post-quantum future
- Cyber resilience of the Netherlands and Europe
- Protection of medical, financial and governmental data
You work on the technology of tomorrow — today.
For who?
You don't need to be a quantum physicist or a cryptography expert. What you do need is curiosity, and a bit of comfort with abstract thinking and mathematics.
This minor is a great fit if you come from:
- ICT / Computer Science
- Mechatronics
- Applied Mathematics
- Applied Physics
- Electrical Engineering
Helpful interests & mindset:
- Analytical, you like digging into how things really work
- Interested in algorithms and mathematical structures
- Curious about security and digital resilience
- Comfortable with abstract thinking
- Excited by 'deep tech' and future-facing technology
- Basic Programming
What you don't need:
- No background in quantum physics required. The essentials are built up within the minor
- No prior experience with cryptography
- No research experience
- No advanced mathematics beyond your current programme
Practical information
The minor is open to students who:
- Are enrolled as a student at Fontys University of Applied Sciences
- Have a background in programming
- Have experience in mathematics, physics, ICT and/or electrical engineering
The necessary quantum and cryptographic foundations are built up within the minor — prior expertise is not required.